
New MacStealer macOS malware steals passwords from iCloud Keychain
A new info-stealing malware named MacStealer is targeting Mac users, stealing their credentials stored in the iCloud KeyChain and web browsers, cryptocurrency wallets, and potentially sensitive files.
MacStealer is being distributed as a malware-as-a-service (MaaS), where the developer sells premade builds for $100, allowing purchasers to spread the malware in their campaigns.
According to the Uptycs threat research team that discovered the new macOS malware, it can run on macOS Catalina (10.15) and up to the latest version of Apple’s OS, Ventura (13.2).
Targeting Mac users
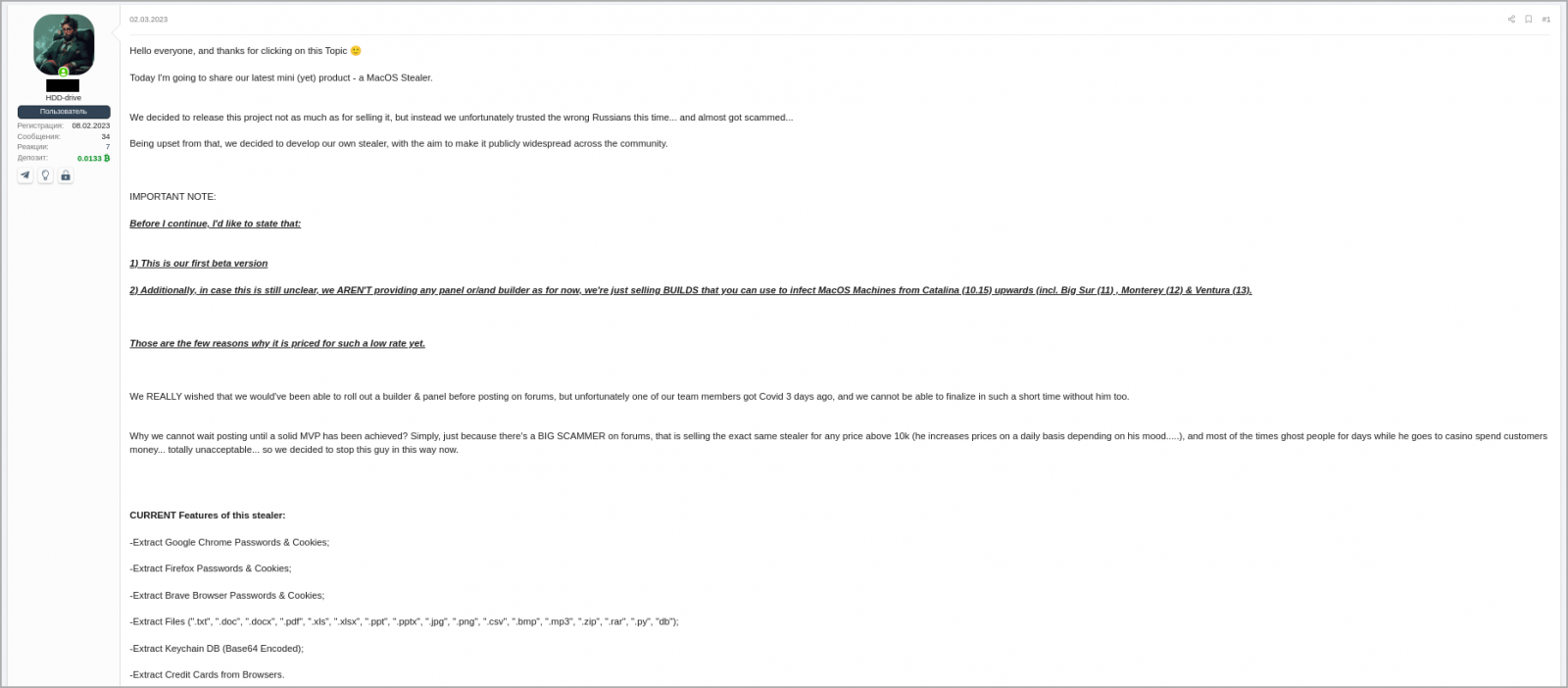
MacStealer was discovered by Uptycs analysts on a dark web hacking forum where the developer has been promoting it since the beginning of the month.
The seller claims the malware is still in an early beta development phase and offers no panels or builders. Instead, it sells pre-built DMG payloads that can infect macOS Catalina, Big Sur, Monterey, and Ventura.
The threat actor uses the lack of a builder and panel to justify the low price of $100 for the malware but promises that more advanced features will arrive soon.
The malware developer claims that MacStealer can steal the following data from compromised systems:
- Account passwords, cookies, and credit card details from Firefox, Chrome, and Brave.
- TXT, DOC, DOCX, PDF, XLS, XLSX, PPT, PPTX, JPG, PNG, CSV, BMP, MP3, ZIP, RAR, PY, and DB files
- Extract the Keychain database (login.keychain-db) in base64 encoded form
- Collect System information
- Collect Keychain password information
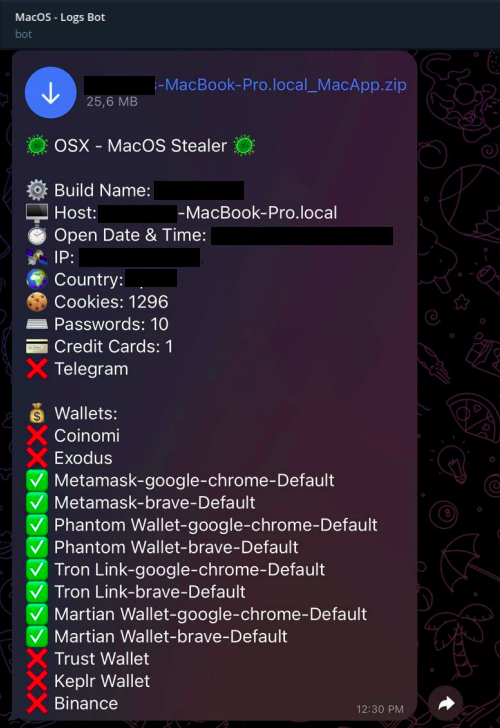
- Coinomi, Exodus, MetaMask, Phantom, Tron, Martian Wallet, Trust wallet, Keplr Wallet, and Binance cryptocurrency wallets
The Keychain database is a secure storage system in macOS that holds users’ passwords, private keys, and certificates, encrypting it with their login password. The feature can then automatically enter login credentials on web pages and apps.
Malware functionality
The threat actors distribute MacStealer as an unsigned DMG file that poses as something the victim is tricked into executing on their macOS.
Upon doing so, a fake password prompt is served to the victim to run a command that allows the malware to collect passwords from the compromised machine.
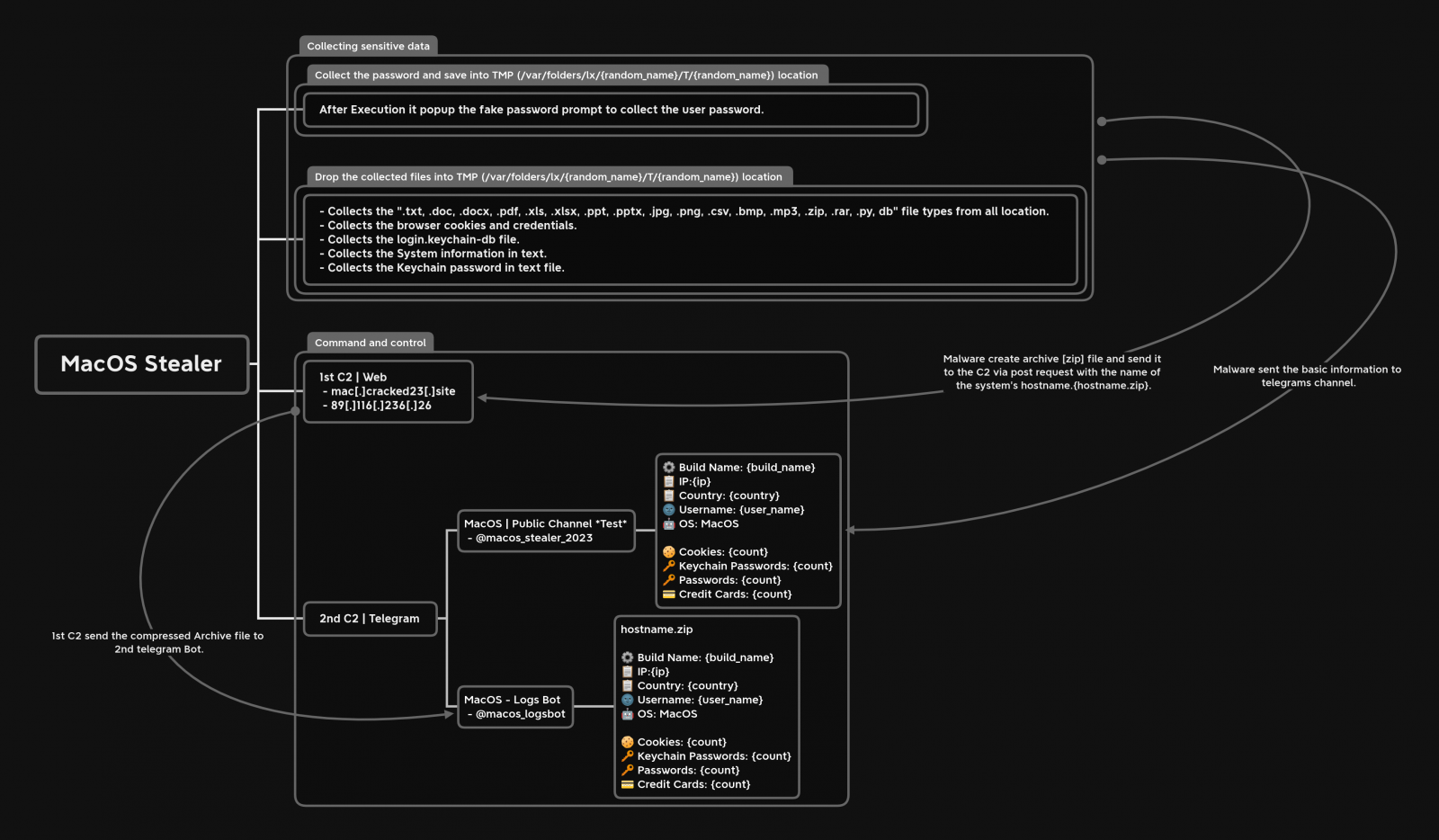
The malware then collects all of the data mentioned in the previous section, stores them in a ZIP file, and sends the stolen data to remote command and control servers to be collected later by the threat actor.
Upon doing so, a fake password prompt is served to the victim to run a command that allows the malware to collect passwords from the compromised machine.
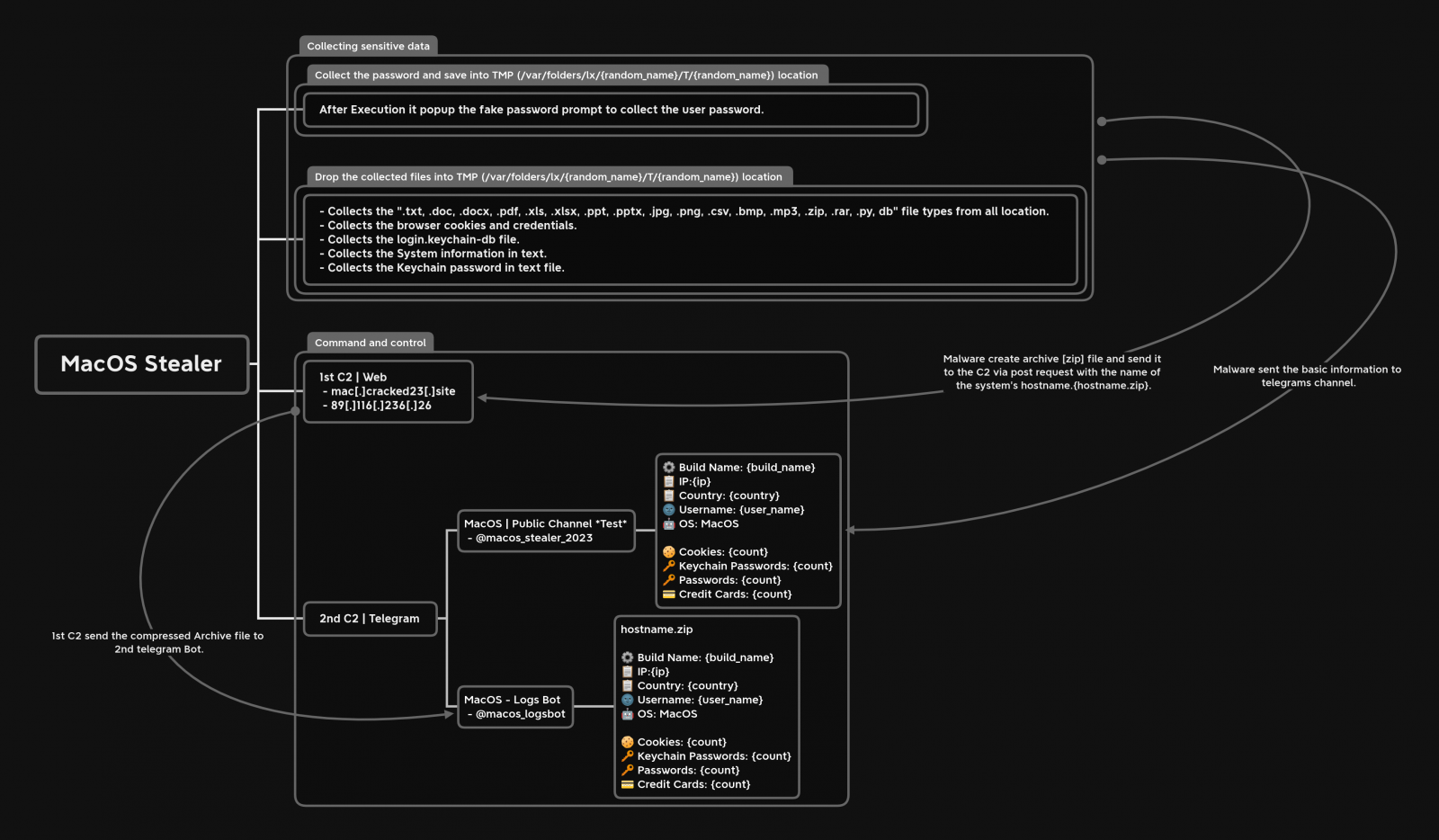
The malware then collects all of the data mentioned in the previous section, stores them in a ZIP file, and sends the stolen data to remote command and control servers to be collected later by the threat actor.
At the same time, MacStealer sends some basic information to a pre-configured Telegram channel, allowing the operator to be quickly notified when new data is stolen and download the ZIP file.
While most MaaS operations target Windows users, macOS isn’t immune to such threats, so its users should remain vigilant and avoid downloading files from untrustworthy websites.
Last month, security researcher iamdeadlyz also discovered a new Mac information-stealing malware distributed in a phishing campaign targeting players of ‘The Sandbox’ blockchain game.
That information stealer also targeted credentials saved in browsers and cryptocurrency wallets, including Exodus, Phantom, Atomic, Electrum, and MetaMask.
With cryptocurrency wallets being highly targeted by threat actors, we will likely see further malware developers targeting macOS in their search for cryptocurrency wallets to steal.
Original Posts: New MacStealer macOS malware steals passwords from iCloud Keychain
